Cyber Security Services and Cyber Risk Management
Managing cyber risk helps your business to be secure, make financial savings and ensure compliance is met with your clients.
Every UK organisation is at risk of a cyberattack, with 7 out of 10 companies falling victim to an attack or breach. UK businesses must adopt a clear cyber-security and risk management strategy, to protect both the company and client data.
It is not a case of whether your organisation is going to be under a cyber attack by hackers, but when. So the million dollar question… what security does your business need?

Our IT cyber security services
Data security is more critical than ever – approximately 60% of small businesses that suffer a cyberattack close down within six months.
At Matrix247, we understand the nature of the threat to the UK’s business community, and that’s why we’ve provided a comprehensive cyber security portfolio to address all your data security needs.
From cybersecurity audits to compliance reviews, our cyber security team is ready to transform how you approach your security. Examine our cyber security portfolio below or contact us to learn more.
Why use Matrix247 for cyber security?
Matrix247 has been ensuring all solutions proposed to clients for the last 2 decades have a security wrap foremost in mind when designing the foundation of any new technologies being implemented.
Being an endorsed supplier to numerous UK Law Societies, Matrix247 are regularly asked to present on many law society panels in providing the very latest advancements available in the world of cyber security.
As well as being accredited to extremely high standards, relationships have been developed with world-class partners to ensure all bases can be covered for our clients wishing Matrix247 to become the sole point of responsibility for managing digital security across the entire ICT landscape.
Matrix247 Cyber Security Portfolio
Prevents and reduces the threat of cyber breaches through leaving back-doors open and easy access to criminals.
Education and awareness with those in, or connected to, your organisation responsible for the existing and continual development of your website.
As this is the most common approach hackers take, this can involve complete staff and management awareness training to ensure all reasonable precautions are being undertaken along with implementing departmental cyber policies as standard procedures to protect your organisations brand.
Should any of your organisations laptops, tablets or mobile devices become compromised, highly accredited forensic teams are available to take digital footprints of devices to track all historic key depressions, deleted data and track data that has been transmitted.
To ensure all your organisations devices remain up to date on the very latest software versions ensuring vulnerabilities found in previous versions are ‘patched’ enabling your organisation to demonstrate compliance if risk assessed.
We can assist and provide appropriate steers to ensure those responsible in your organisation for GDPR compliance are always adhering to the very latest changes in company and client data protection.
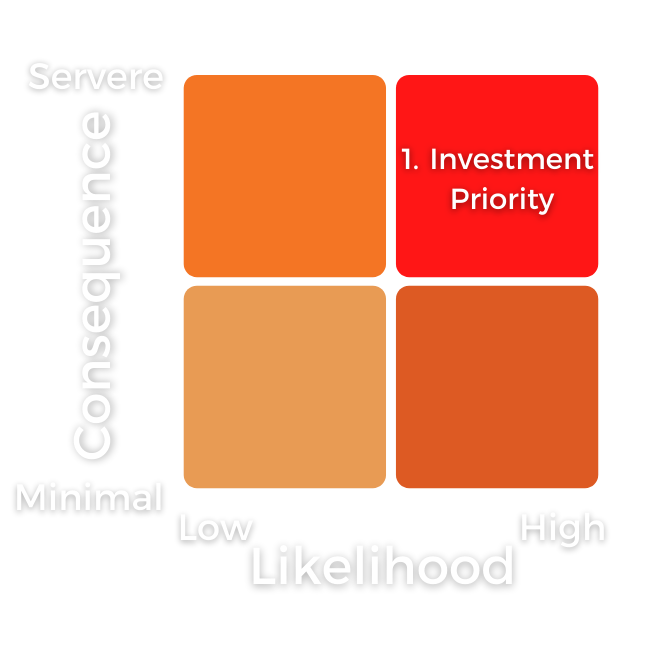
To ensure all current operations (this may involve your organisations infrastructure, website applications, social media feeds, physical hardware and wireless connectivity) are secure to the levels expected for your organisations investment in security. Using ethical hackers we will essentially engage in an authorised cyberattack to evaluate your level of security. In doing so, we can determine the vulnerable parts of your organisation – allowing us to propose the optimum cyber-security solution for you to consider taking the risk verses consequence verses investment table above into account as we work with you.
Ensuring behind all administrator portals on all applications across your organisation no doors have be left potentially ajar through human error by either suppliers or internal staff with existing or historic access rights.
The most advanced platforms are available to be constantly remotely monitoring your Wide Area Network (WAN) and LAN (Local Area Network) infrastructure and provide triggered alerts to both ourselves and those with access rights to detect all potential issues before occurring and so avoiding costly downtime and staff, management and customer frustrations.
This is the certification we would recommend ALL organisations should be striving to achieve and keep in place with annual reviews. It’s an essential checklist that can be simply applied across your complete estate to ensure that awareness of risks are clearly in place and it’s documented as to what, if any, level of security has been applied. If you wish to self-assess, you can get the logo without the PLUS addition. If you have been successfully independently assessed by an approved CE+ assessor, then you can use the complete logo. This is telling all your company management, shareholders and investors and most importantly your clients and suppliers that you take the security of their data very seriously and keep an annual review alive.
Let Us Protect your Business from Cyber Attacks Today
How important is cyber security for businesses?
Cyber security is not a part of your business’s functions but a part of your business’s success. The risk of attack is more significant than ever, with the UK government estimating businesses suffered 7.78 million cyberattacks of all types in 2023.
Today, investing in cyber security is the cost of doing business in the UK and abroad. Unsure whether you need to pay more attention to your business’s security protocols?
The chances are you are more vulnerable than you think. Here’s why cyber security powers the success of UK firms today:
- Every organisation uses IT systems to function. Our dependency on technology brings tremendous benefits but also creates enormous security gaps. Cyber security empowers your firm to leverage technology without incurring the risk that comes with it.
- Data is your most valuable asset. Cyber security preserves your data quality and keeps your business operations moving.
- Cybercrime is growing unabated. Each year posts record figures, with new attack vectors outwitting companies and bringing them to their knees. Whether malware or ransomware, your business must move quickly enough to keep up.
- Government regulations legally require you to meet minimum cyber security standards. Moreover, if you operate abroad, you’ll have to comply with both national and global standards, including the EU’s General Data Protection Regulation (GDPR).
- Your customers and business partners have higher expectations than ever. Fail to protect their privacy, and you risk losing a hard-won reputation built over many years in seconds.
Cyber security is one of the foundations of business success in the modern business landscape. Paying attention to your cyber security measures is an ongoing task that must be classified as just as important as hiring employees and providing customer service.
Benefits Delivered
Peace of Mind
Your security is managed by an established team of experts, part of the top 1% of worldwide businesses with the ISO accreditation.
Supply Chain Security
Ensuring data and client information through the supply chain remains extremely secure at all times.
Reduced Downtime
Keep all communication to clients & staff operative at all times without running the risk of cyber breaches occurring.
Save Management Time
Most organisations in the public and professional services sector must report all breaches to regulatory bodies to comply the regulations and make affected clients aware.
Save Money
Reduce the risk of paying large fines to regulatory bodies in not being able to demonstrate a reasonably comprehensive cyber security policy.
Brand Reputation Protection
Public companies must announce breaches to all share/stake holders. Large investments by organisations in building a solid brand reputation over years can suffer huge overnight financial loss.
What aspects of cyber security should businesses be aware of?
Maintaining a secure environment means understanding the basic principles of cyber security. All solutions operate on these principles to address specific threats.
Businesses establishing cyber security protocols for the first time must bear these five principles in mind:
- Confidentiality – Confidentiality is the first element of your security. It means keeping all sensitive information, including customer and financial data, safe and secure through methods like password protection, access controls and encryption.
- Integrity – Integrity guarantees that the data you protect is accurate and complete. Organisations must ensure that their data has not been altered or tampered with by implementing techniques like checksums and digital signatures.
- Availability – Cyber security isn’t like a bank vault. Your data must be protected, but it should remain available to your team so that they can do their job. It’s the key to preventing downtime and maximising your productivity.
- Authentication – How do you tell the difference between authorised and unauthorised users? The fourth element of authentication provides the tools to allow the right people in and keep the wrong ones out. Examples include passwords, smart cards and biometrics.
- Non–Repudiation – Non-repudiation creates a paper trail that assigns a particular action to a particular user in a way that they cannot deny. The most common way to do this is through digital signatures. It may seem like a small thing, but this is a matter of forcing users to take responsibility for their actions.
Achieving these five elements balances the need for security and compliance with productivity and efficiency. Accelerate your business’s security standards without hindering your ability to do your job.
Cyber security threats to businesses
Tabloids often focus on the type of attack and the end result. Your business may face phishing, malware, ransomware and insider threats, but these are attack vectors, not the source of your vulnerability.
Is your business prepared for threats from cybercriminals? You might be surprised that these are the most common vulnerabilities faced by companies in the UK:
- Weak passwords
- Stolen credentials
- No encryption
- System misconfigurations
- Outdated software
- Zero-day vulnerabilities
- Low-quality input sanitisation
- Insider threats
- Poor access controls
- Vulnerable APIs
The challenge of confronting these threats is that while you can address them quickly, any fixes are not permanent. The moment you take on a new employee, postpone a software update, or upgrade your systems, these threats can rear their heads again.
It underpins the need not only to familiarise yourself with these threats but to enlist a cyber security expert like Matrix247 to oversee your security measures and support your business as it moves from one chapter to another.
Measuring Risk Priority Vs Consequence Vs Investment
Like insurance policies, the more you invest, the more security cover you put in place.
The key is assessing the risks of occurrence and simply categorising whether a high, medium or low risk for a start. Firstly take the high-risk with high consequence as this is the top right quadrant. Assess the investment need for each element that can be covered and weigh up the minimum investment that should be deployed depending on your organisation, the data you are protecting and cost incurred with the consequence.
Cybercrime – Threat to your business success
New figures suggest that half of British businesses lack the skills to protect themselves against cybercrime. At Matrix247, we understand that you aren’t a cybersecurity expert, nor should you be.
The immense threat to everything you have built cannot be underestimated, but most people lack the skills, education, and will to become cybersecurity experts themselves. By hiring a professional cybersecurity company, you outsource the problem and acquire guaranteed results.
Contact Matrix247 to learn more about how we can neutralise this threat to your business success today.

Speak to our Cyber Security experts today
Call our team and you’ll speak to someone who really understands our products and can give you an estimated quote, no hassle, no obligation.
A named and dedicated account manager will allocated to you, and provide a consultative approach to help find the right solution for your organisation.
Call us on 0345 030 5601 or, alternatively fill in the form and we can call you back.




